Description
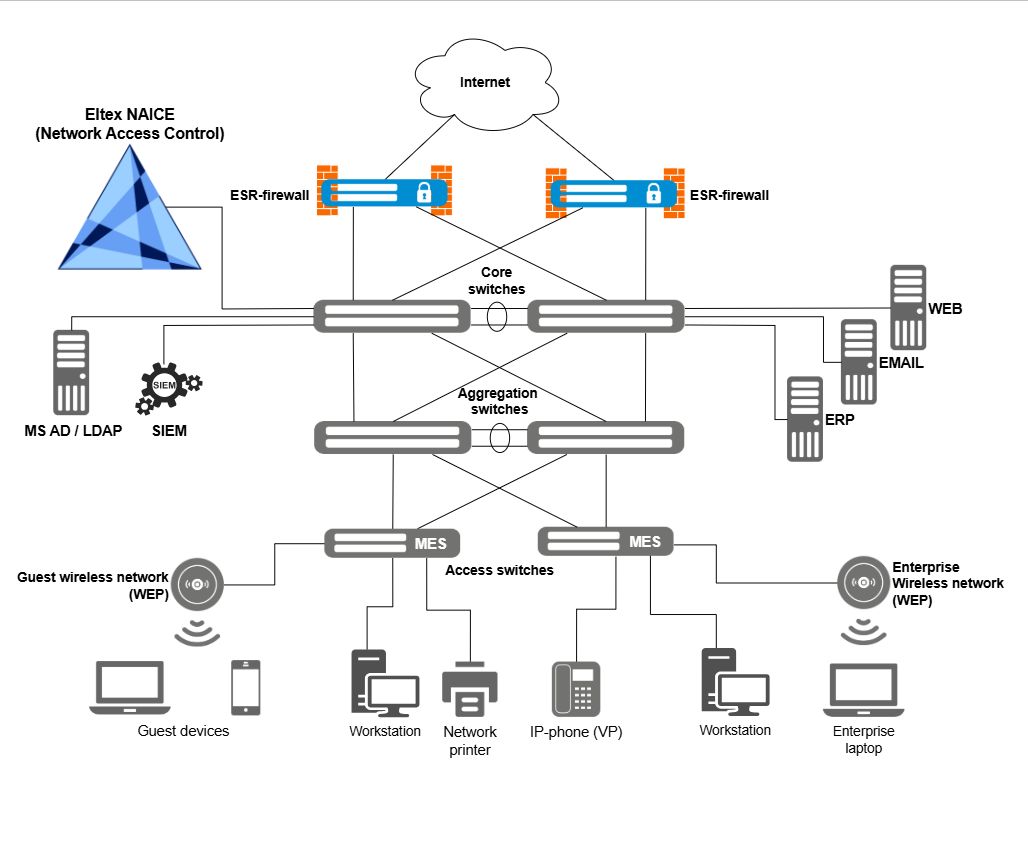
NAICE (Network Access and Information Control Engine) is a software system that provides centralized management of user rights to access the network and its resources.
Administrators get flexible tools to create and implement access policies for various network resources such as servers, printers, etc. Feature-based segmentation allows efficient management of client connections and ensures network security.
NAICE is a multi-vendor solution that supports interaction with RADIUS compatible devices from different manufacturers.
Functions
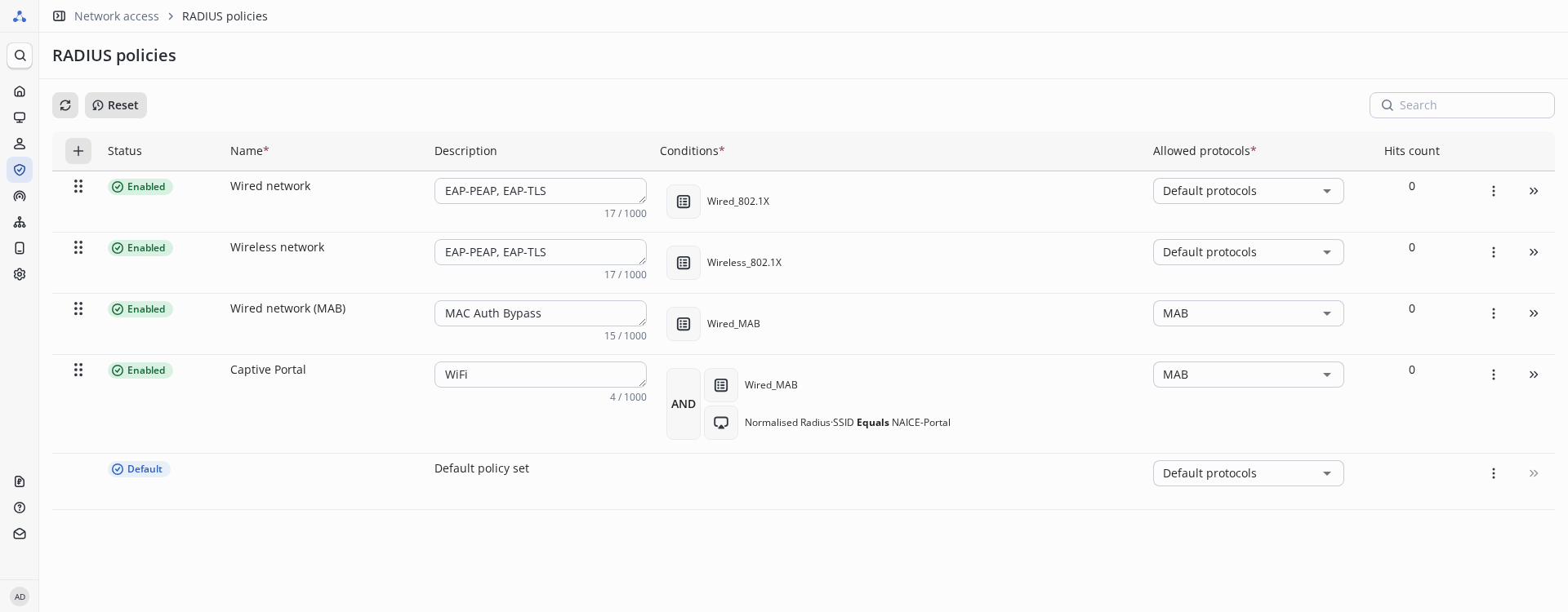
Policy sets provide effective control of connections to network resources. The system performs identification, authentication and authorization of users, making it possible to assign rights according to a variety of parameters. This allows flexible segmentation of network and device access, which significantly increases network security.
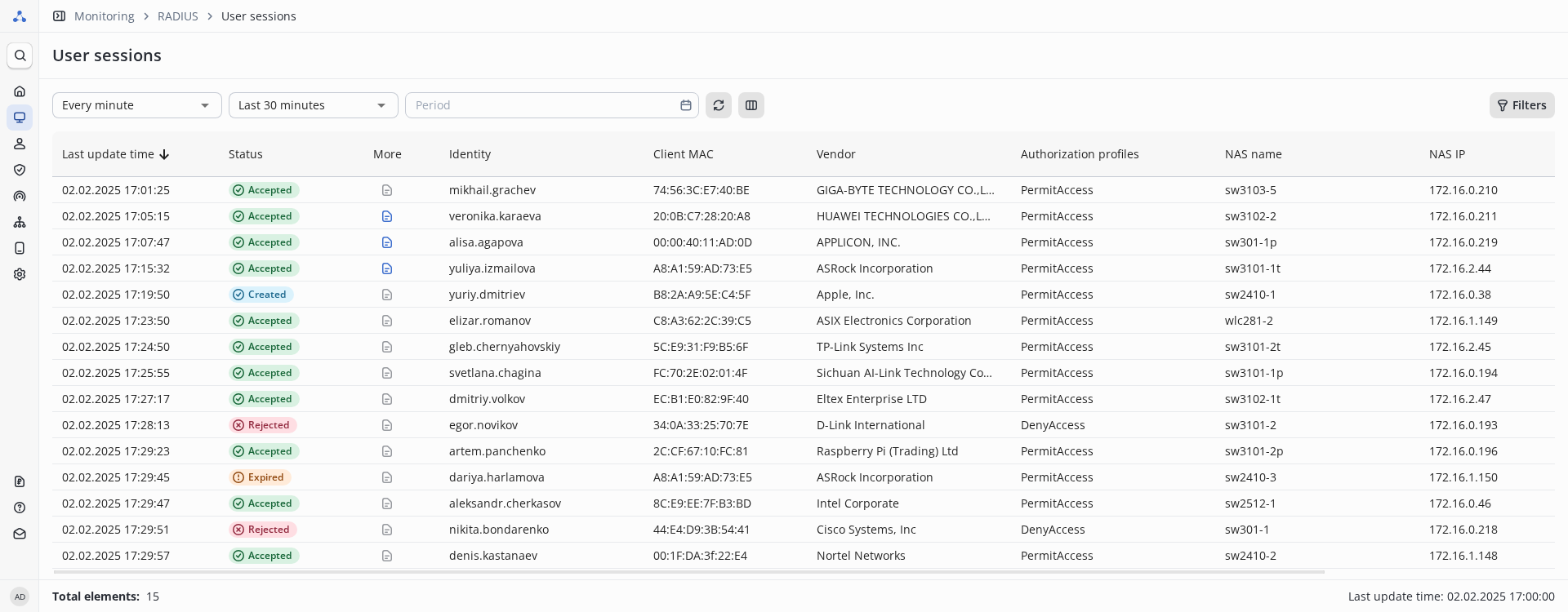
Monitor device connections to an enterprise network with logs. The system logs factors affecting the granting or denial of access, so that connection failures can be quickly detected and resolved.
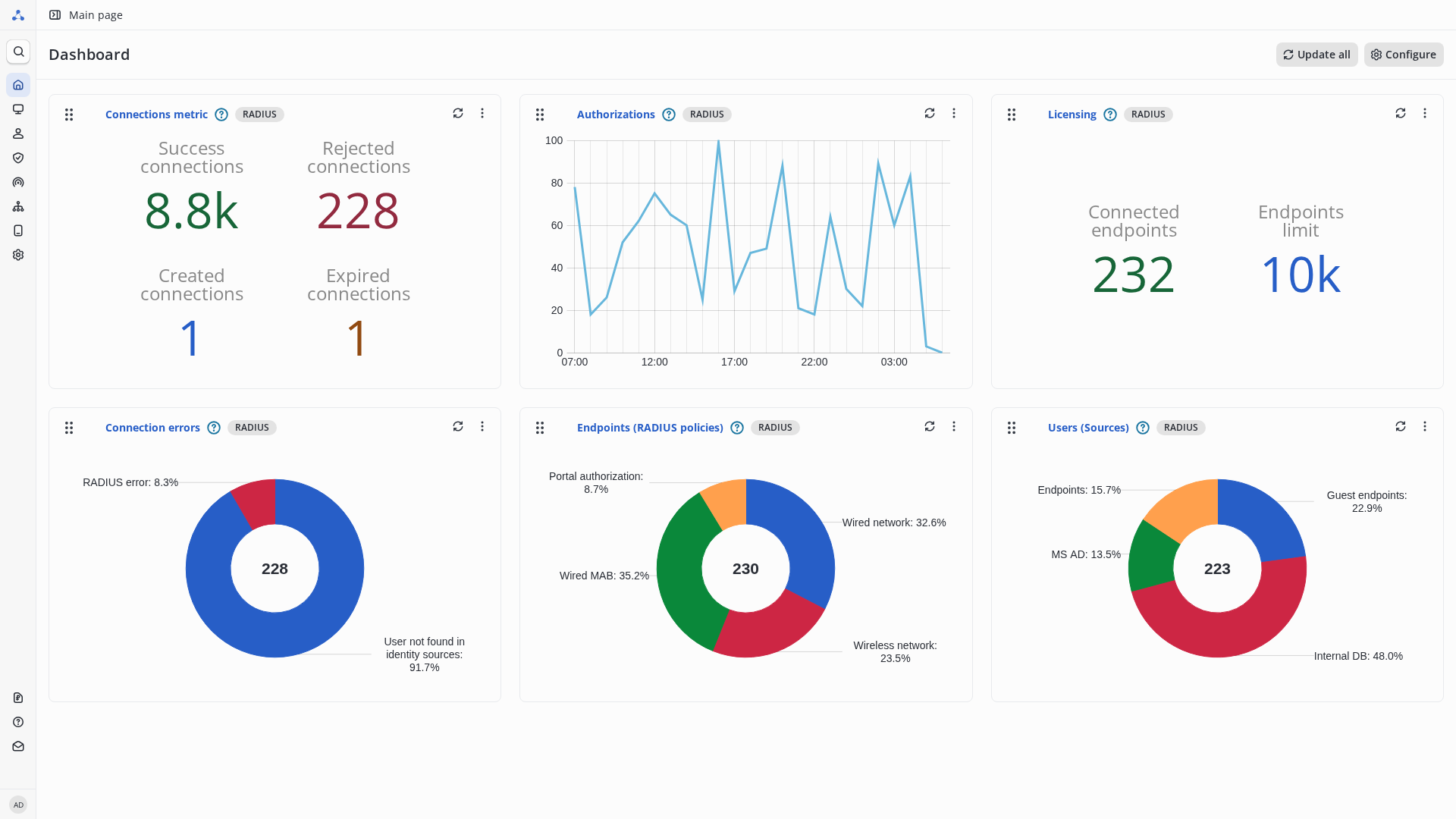
A comprehensive access control system based on the RADIUS protocol provides reliable user authentication and authorization, network connection management and protection against unauthorised access to the network via the IEEE 802.1x protocol (EAP-PEAP).
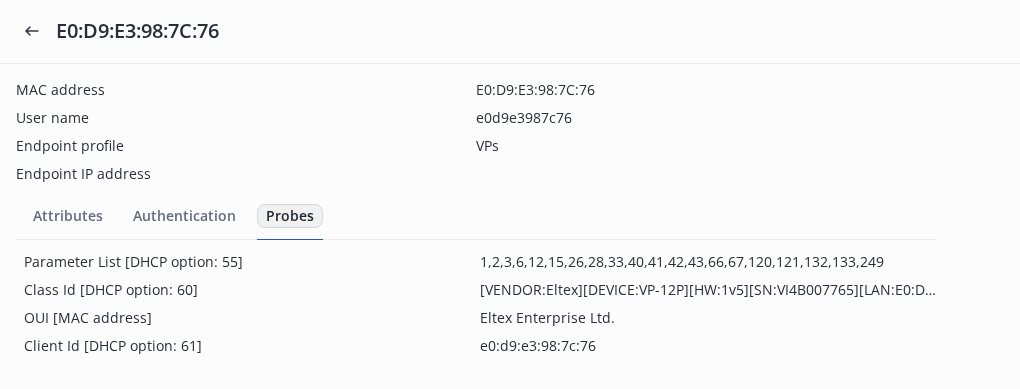
The feature provides fast and secure addition of non-IEEE 802.1X devices (printers, cameras, IoT devices) to the network. Identification and access are performed by MAC addresses based on assigned policies. Profiling identifies the type of device and its specifications for the subsequent application of appropriate access rules.
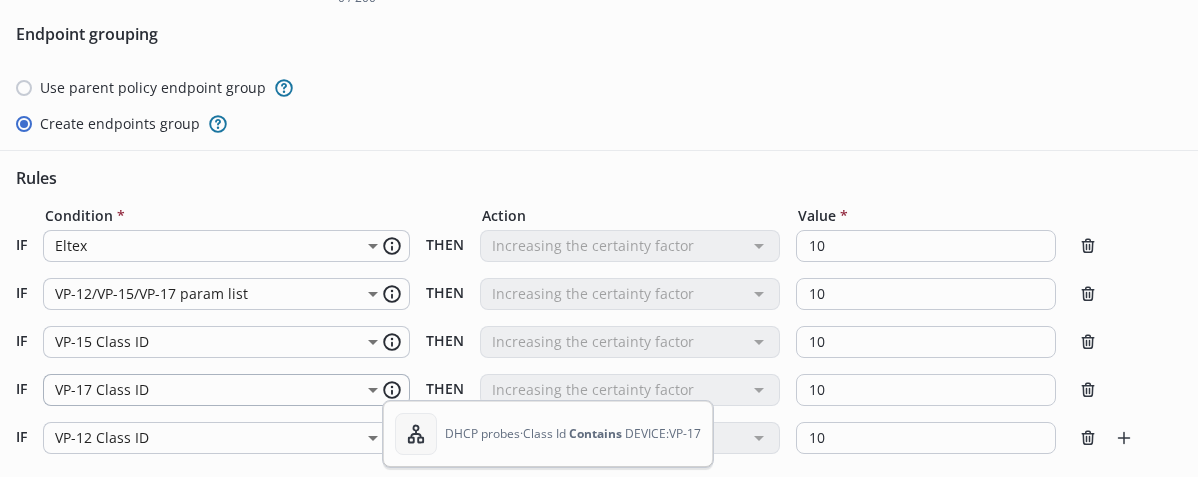
Profiling using MAC-OUI and DHCP probes allows automatically determine the type of connecting devices, assign its a profile and group in accordance with configured policies, prevent device substitution, and quickly identify unauthorized connections.
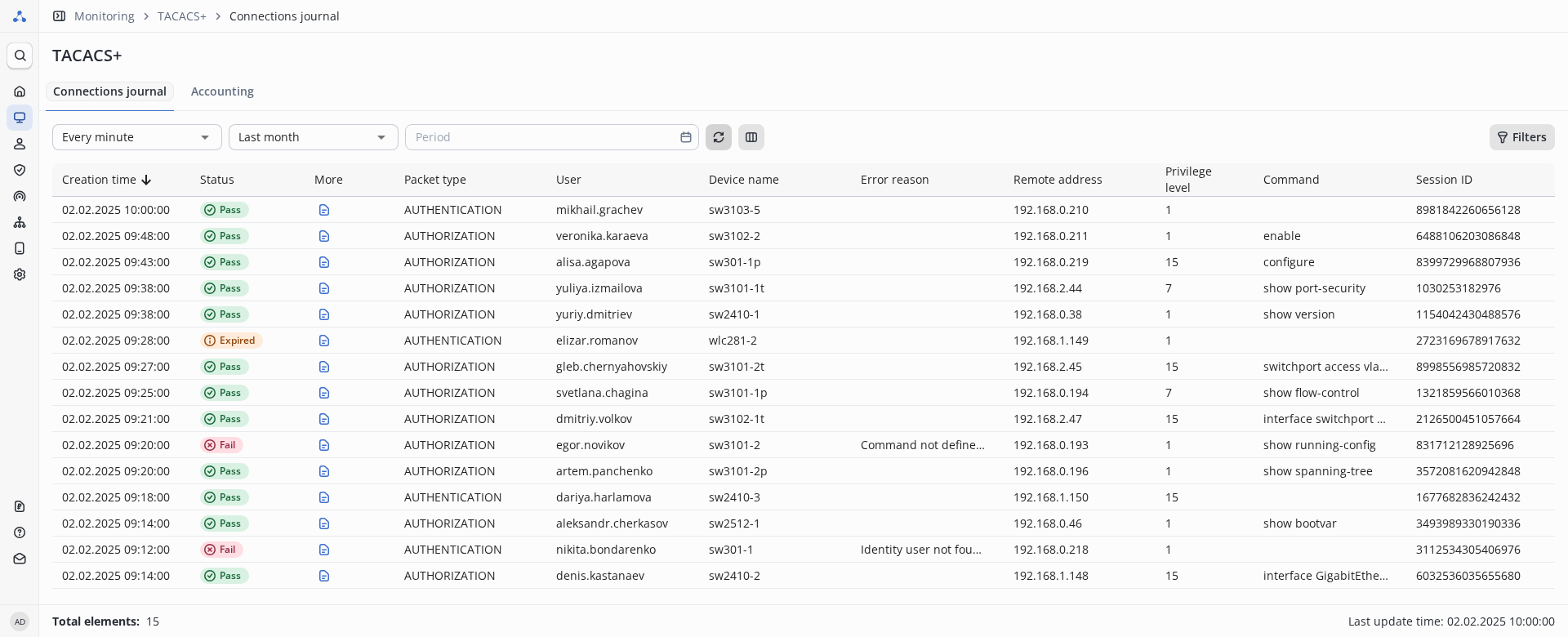
Access control via the TACACS+ protocol provides the following capabilities:
- Authentication and authorization of network device administrators via the TACACS+ protocol with a specified privilege level;
- Authorization and accounting of network device administrator commands via the TACACS+ protocol;
- Sending TACACS+ accounting in syslog format to a third-party server (via Syslog).
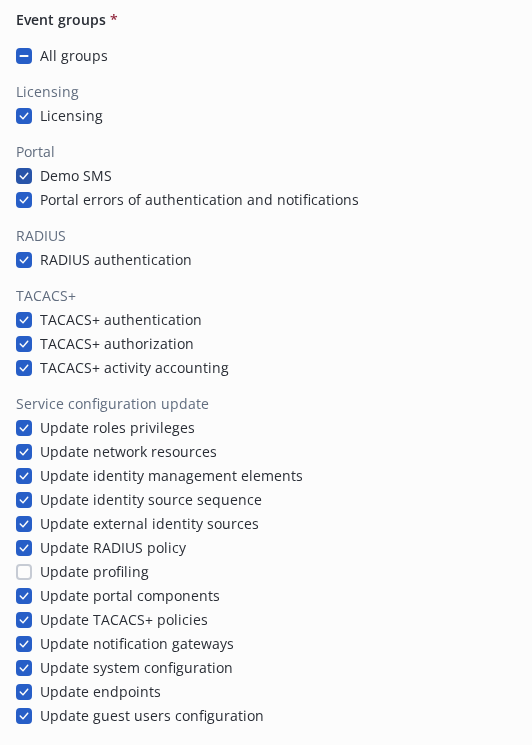
In NAICE, authentication and authorization events can be sent to external SIEM systems for centralized analysis and correlation with data from different sources. This helps timely identify complex attacks on network resources and automate their detection processes
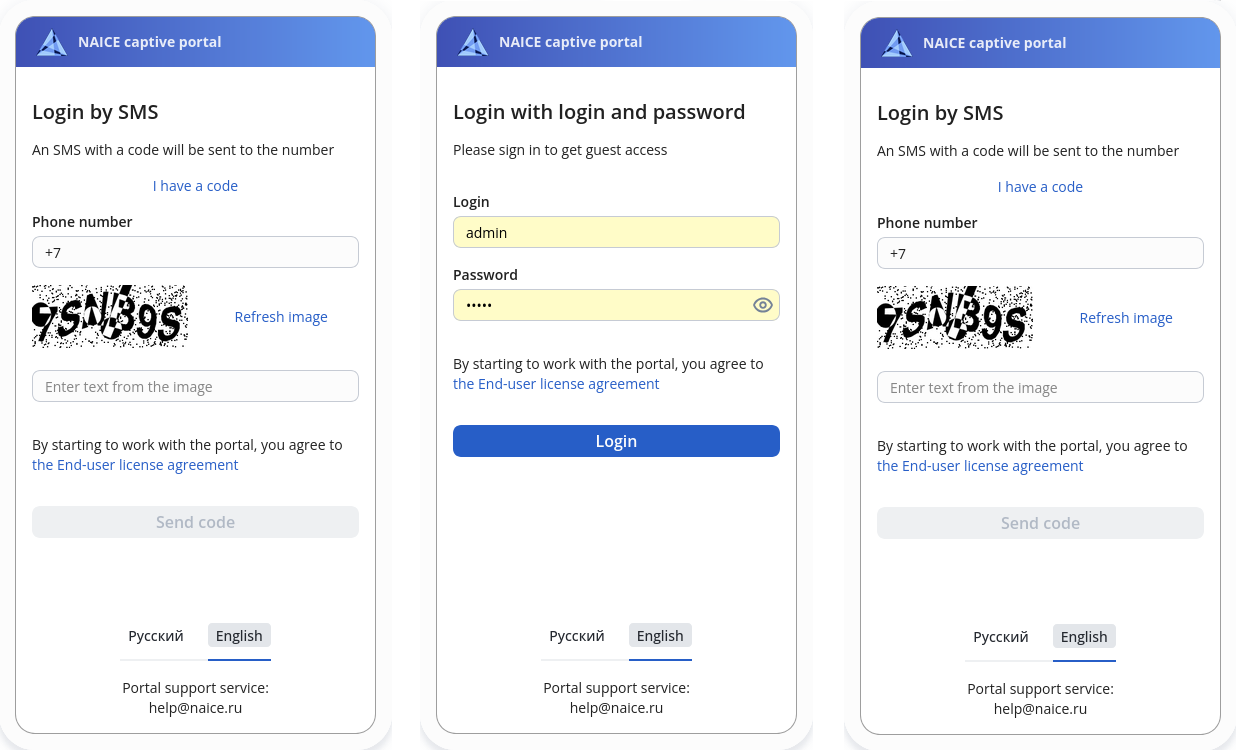
NAICE provides a guest network access service (Captive Portal). User authentication is available both via SMS and via accounts from external identity sources (MS AD, LDAP) or a local database. To comply with the corporate style, there is a built-in portal authorization web page designer.
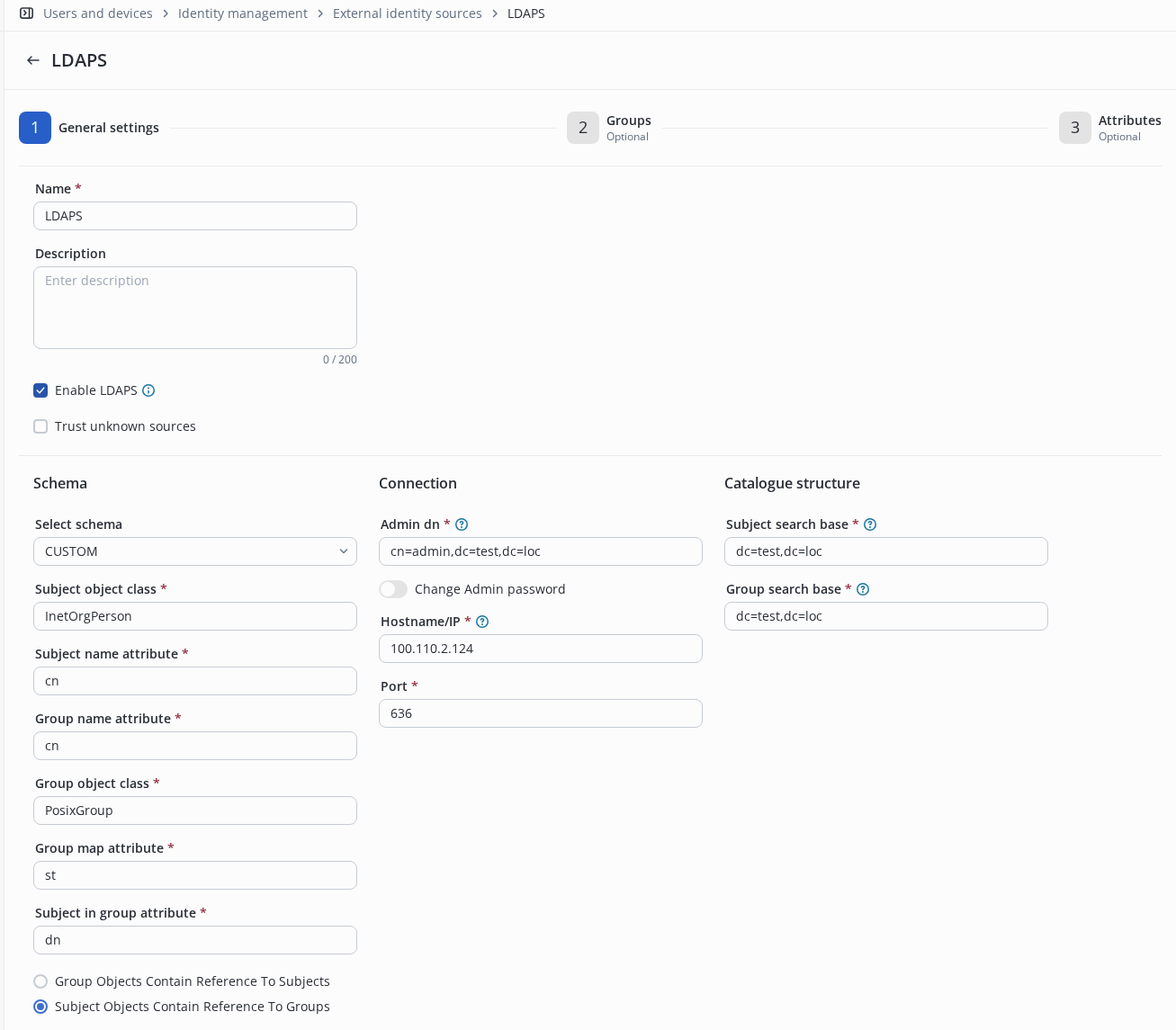
NAICE is integrated with the user database, their attributes and groups from/to Microsoft Active Directory (MS AD) and LDAP. This provides user identification, authentication and authorization based on data from a centralized directory service without the need to change credential storage infrastructures. Depending on an attribute from the directory, such as VLAN or ACL membership, the corresponding access policy is assigned.
Documents and files
Version 1.1.1
Features
- Displaying the hostname that processed the request in RADIUS/TACACS+ logs
- Managing PostgreSQL replication manager parameters through Ansible playbook variables
- Running Ansible playbooks from Astra Linux 1.8 and RedOS 8 hosts
Bugfix
- Saving Account settings for system users from an external source
- Handling backend services restarts in the WEB GUI.
Version 1.1
Features
- Some system settings are now available in the NAICE web interface, significantly simplifying the configuration process and reducing the need to use environment variables — this is the first step toward simplifying system management.
- Password policies - customizable password complexity requirements for system users
- Integration with an SMTP email server (notification gateways) for sending notifications when system users are created or their credentials are changed
- Support for downloading trusted SSL/TLS certificates in the WEB interface
- Login to the NAICE WEB interface using an account from an external identification source (MS AD and LDAP)
- Support for setting roles in the NAICE WEB interface using account attributes from an external source
- Support for LDAPS when working with an external identification source
- Support for downloading trusted SSL/TLS certificates in the web interface
- CA certificate verification when sending SMS via the HTTPS notification gateway
- Support for downloading trusted SSL/TLS certificates in the web interface
- Integration of NAICE with Peeper 0.8 - monitoring system for Eltex software products
- Distribution as a QCOW2 image
- Deploying NAICE with redundancy without VRRP
Enhancements
- Managing accounts from external MS AD and LDAP authentication sources has been moved to a separate service to prevent interference between RADIUS and TACACS+ services.
- Substitution of a RADIUS User Password with an arbitrary attribute value from an external MS AD and LDAP source.
- Cloning of RADIUS and TACACS+ authentication and authorization policies.
- Endpoint counting (license restrictions) - the solution's dependence on mandatory attributes has been reduced to support a wider range of equipment.
- An event for unsuccessful user authorization has been added to the Log.
- The ability to store personal account settings in the system has been added: selected language and time zone.
- Dashboards now display the records number and retention period for RADIUS and TACACS+ logs, namely:
- RADIUS sessions
- TACACS+ sessions
- TACACS+ accounting
Bugfix
- Displaying the privilege level and identity source at TACACS+ Connections journal
Previous versions
Version 1.0.2
Features
- The public naice-radius certificate used for EAP-PEAP authentication has been updated
- Ansible playbook to replace naice-radius certificates used for EAP-PEAP and EAP-TLS authentication
Version 1.0.1
Features
- Support for using the domain prefix in the MS AD userPrincipalName attribute
- Support for MS AD domain computer password rotation
Enhancements
- Improved the algorithm for selecting the priority MS AD controller
Bugfix
- Work with the RADIUS database cluster and system events
Version 1.0
Features
- Role-based access control (RBAC) for system users
- Integration with SIEM systems for security events logging
- Logging of system user actions
- Logging and storing endpoint sessions in the database
- Distribution as an OVA image, with a web panel for quick and easy NAICE configuration
Enhancements
- Update PostgreSQL major version from 15 to 17
- The web interface has been redesigned to use Protocol UI
- Authorization profile cloning
Version 0.9.1
Features
- NTLMv2 support
- Machine EAP-TLS authentication support
Enhancements
- Eltex dACL attributes support
- Huawei RADIUS attribute dictionary has been updated
Bugfix
- Manually adding an endpoint with a randomized MAC
Version 0.9
Features
- Portal authorization support
- SMS authentication on the portal
- Portal authentication using logins/passwords of previously created accounts in the system or from external identification sources such as LDAP and MS AD
- NAICE installation for isolated network (Air gap)
- Import/export in CSV format of entities such as:
- Network users
- Network user groups
- Endpoints
- Endpoint groups
- Network devices
- Network device groups
- Administrators TACACS monitoring widgets
- External logging system based on Loki and Grafana
Version 0.8.1
Features
- Logging and storing TACACS+ Accounting in the database
- PLR (Permanent License Reservation) licensing method
- HTTP proxy support for connecting to Online ELM
Version 0.8
Features
- TACACS+ protocol support
- Ability to send information Logging of executed commands (accounting) via the Syslog protocol to an external server.
- Support for authentication sources from MS AD and LDAP
- Widgets for monitoring RADIUS connections
- Demo mode for testing software without license installation
Enhancements
- Interaction with the MS AD directory service
- Without installing additional software
- Simplified configuration of an external AD source
- Addition of multiple AD sources with different domains
- NAICE update process from version to version
Version 0.7
Features
- Licensing using the Eltex License Manager (ELM) license server
- License based on the number of successfully authorized unique endpoints per day.
- Two licensing methods are supported: online and offline.
- EAP-TLS authentication with OCSP support for checking certificate revocation lists.
- HTTPS support for public interfaces, with the option to use your own certificate or a self-signed one.
- Active-Active redundancy on two nodes.